“Protect the Cyber”: The WannaCry Ransomware Attack
“As cybercriminals become more sophisticated, there is simply no way for customers to protect themselves against threats unless they update their systems.” — Brad Smith, Microsoft President/CLO
— Brad Smith, Microsoft President/CLO
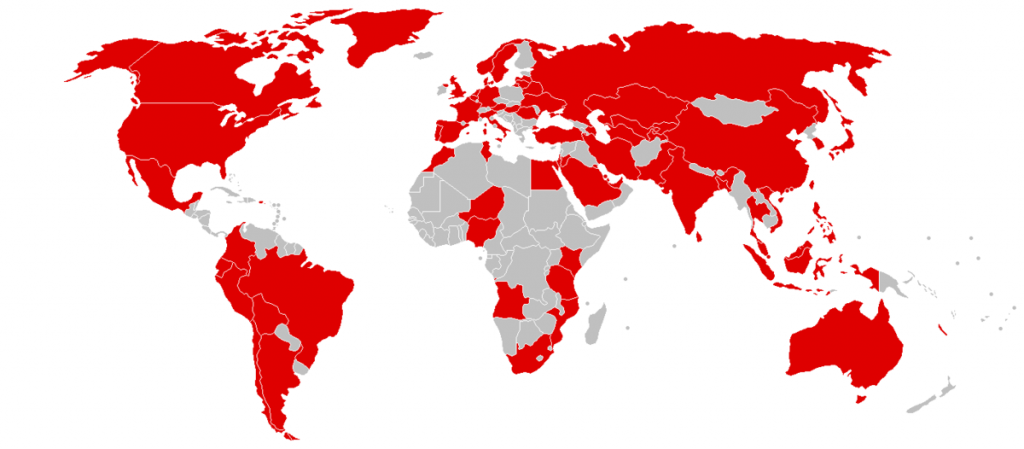
A devastating malware attacked called “WannaCry” (aka “WannaCrypt”) was introduced to the world on Friday, May 12, infecting roughly 57,000 computers in over 150 countries that same day. As of Monday morning that estimate had risen to at least 200,000. WannaCry is designated as “ransomware,” meaning its intent is to extort money from its victims. The virus reportedly encrypts data on affected machines and asks users to pay said ransom in Bitcoin in order to access their data again. On Saturday, a 22-year-old UK researcher discovered a “kill switch” that helped slow the spread of the ransomware by registering a previously nonexistent domain name that was being pinged by the virus.
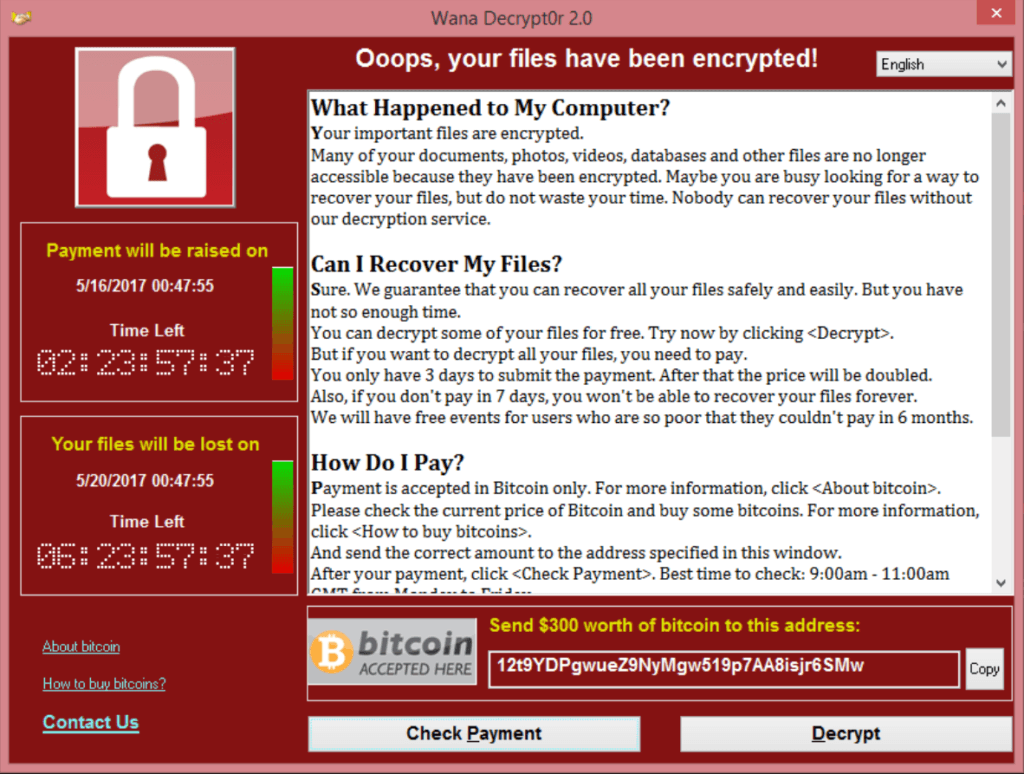
Ironically introduced a day after the president’s executive order on improving federal cybersecurity, the attack was the result of a vulnerability in Microsoft Windows operating systems discovered by the National Security Agency (NSA). While the software was patched two months ago (according to Microsoft’s own security release notes), the NSA’s information regarding it was subsequently stolen and published online by the Shadow Brokers back in April. Of particular note were the EternalBlue and DoublePulsar software developed by the NSA to exploit this flaw.
“This attack provides yet another example of why the stockpiling of vulnerabilities by governments is such a problem,” wrote Brad Smith, Microsoft’s President and Chief Legal Officer, in a blog post on Sunday. “We have seen vulnerabilities stored by the CIA show up on WikiLeaks, and now this vulnerability stolen from the NSA has affected customers around the world. Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage. An equivalent scenario with conventional weapons would be the U.S. military having some of its Tomahawk missiles stolen.”
Smith’s position and sharp criticism reminded many of the 2016 debate between Apple and the Federal Bureau of Investigation (FBI) regarding the iPhone of the December 2015 San Bernardino shooting suspect. “The United States government has demanded that Apple take an unprecedented step which threatens the security of our customers,” CEO Tim Cook wrote in February 2016. “We oppose this order, which has implications far beyond the legal case at hand.” Judging by the scope of last weekend’s attack — which, for example, affected Britain’s National Health Service (NHS), FedEx in the U.S, and Spain’s Telefónica — some would argue that Cook was correct.
Regardless of the blame game, however, a series of events occurred that led to the broad scope of the attack in the first place:
- The existence of the vulnerability
- The NSA’s discovery and weaponization of said vulnerability
- Microsoft’s patch in March
- The Shadow Brokers’ hack and information dump in April
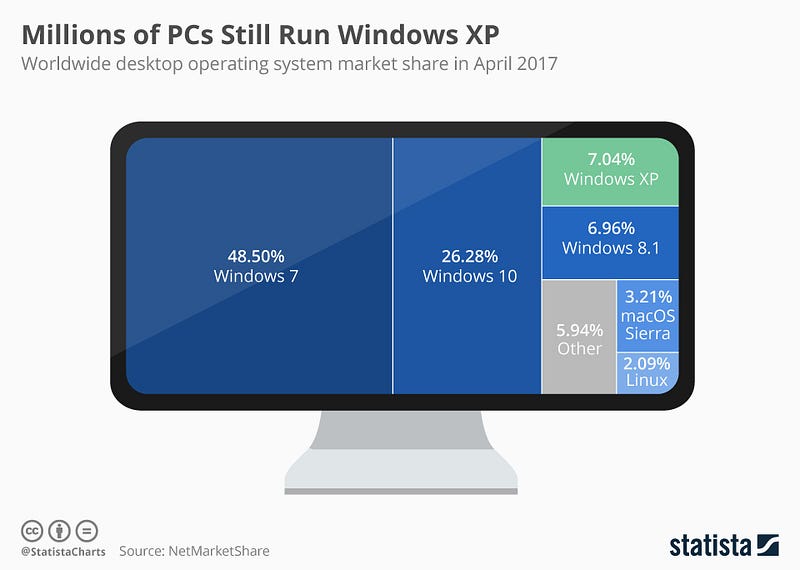
Even with the points outlined above, the most important one was this: Nearly all of the affected end users and/or organizations did not have the security update from two months ago. What’s more, most of the affected machines were running either Windows XP or Windows 7, which were released in 2001 and 2009 respectively. Full support for XP ended in 2014, while mainstream support for 7 ended in 2015 (full 7 support will be ending in 2020). According to NetMarketShare, Windows 7 is still the most popular operating system in the world, currently running on 48.50% of computers; XP is still run on just over 7%. The WannaCry attack forced Microsoft to issue a security update to XP after its life cycle ended — something they would normally have charged for if lives were not literally at stake.
Smith also made the following point in his blog post: “This attack demonstrates the degree to which cybersecurity has become a shared responsibility between tech companies and customers.” If you would like to know how to protect your systems from this or other viruses, WIRED has a detailed breakdown on how to do so. In this day and age, the more we fail to keep our technology and security as up to date as possible, the more we place our very lives at risk.